每次固件安装,均需要重启系统【系统》重启】,这重启动方式最彻底。
1.下载固件
原先系统为v2.1.28,从zidoo.tv官网下载v2.1.45的最新固件包,并存在百度云盘。
通过网盘分享的文件:zidoo-x9s固件
链接: https://pan.baidu.com/s/1CBj2I2ggl0h_5Dt4wM2nSA?pwd=2tgi 提取码: 2tgi
2.安装固件
第一步:升级至最新固件v2.1.45,以及最新的oenwrta-18.06的openwrt固件包。
第二步:安装RealtekAdbdAuto-v1.1.0-signed.apk和RealtekOpenwrtDNS-v1.0.0-signed.apk,前者是adbd的调试开启,后者是DNS的执行,若不开启是无法安装执行路由解析的如ping baidu.com命令是无法完成百度地址的转换。
安装包完后,重启系统。
3.静态化IP地址如192.168.0.110。
4.访问http://192.168.0.110网页,不用设置密钥,以防忘记。
a).添加公钥,采用证书方式访问。【系统 》管理权 》SSH访问】。
b).添加软件源。【系统 》管理权 》软件包》配置》自动义软件源】添加如下:
src/gz openwrt_core https://mirrors.cqupt.edu.cn/openwrt/releases/23.05.3/targets/YOUR_TARGET/aarch64_cortex-a53/packages
src/gz openwrt_base https://mirrors.cqupt.edu.cn/openwrt/releases/23.05.3/packages/aarch64_cortex-a53/base
src/gz openwrt_luci https://mirrors.cqupt.edu.cn/openwrt/releases/23.05.3/packages/aarch64_cortex-a53/luci
src/gz openwrt_packages https://mirrors.cqupt.edu.cn/openwrt/releases/23.05.3/packages/aarch64_cortex-a53/packages
src/gz openwrt_routing https://mirrors.cqupt.edu.cn/openwrt/releases/23.05.3/packages/aarch64_cortex-a53/routing
src/gz openwrt_telephony https://mirrors.cqupt.edu.cn/openwrt/releases/23.05.3/packages/aarch64_cortex-a53/telephony
5.挂载硬盘,务必确认硬盘是否挂载成功,设备地址是以/dev/xxx,但默认挂载地址是以/mnt/xxx形式,故输入地址时,请检查正确。
6.设置挂载盘随系统启动
方法一:添加启动项。【系统 》启动项 》 本地启动脚本】添加
mount -t vfat /dev/sda1 /mnt/sda1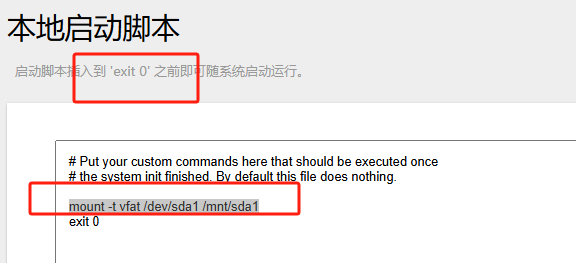
方法二:编写挂载脚本:假如路径为/data/mysda1.sh,其内容如下:这方法行不通
uci add fstab mount
uci set fstab.@mount[-1].device='/dev/sda1'
uci set fstab.@mount[-1].target='/mnt/sda1'
uci set fstab.@mount[-1].fstype='vfat'
uci set fstab.@mount[-1].enabled='1'
uci commit fstab
检验/etc/config/fstab文件内容,已经在尾部添加如下代码:
config mount
option device '/dev/sda1'
option target '/mnt/sda1'
option fstype 'vfat'
option enabled '1'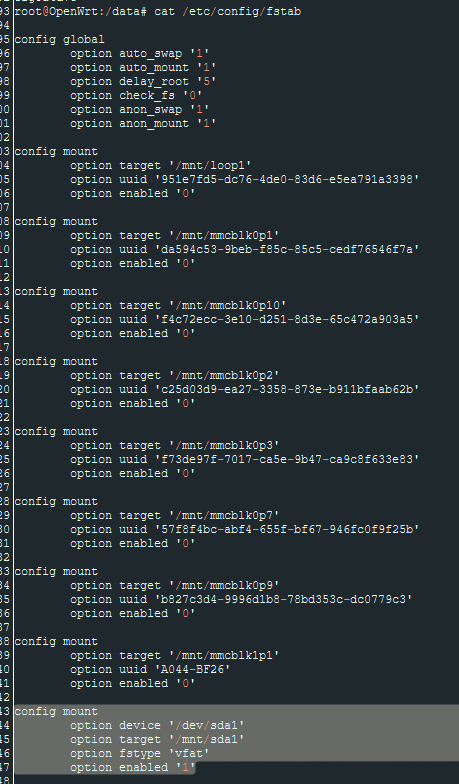
6.开启nas服务。
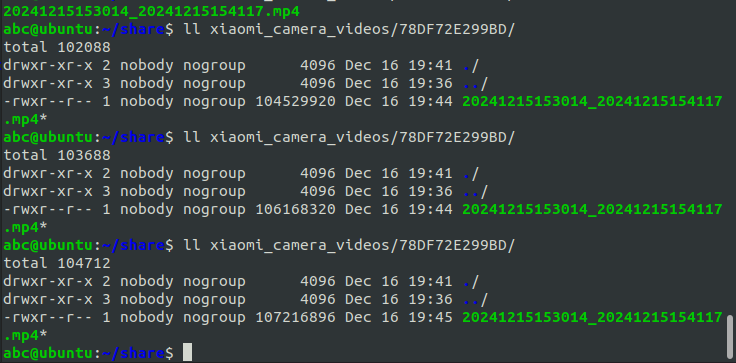
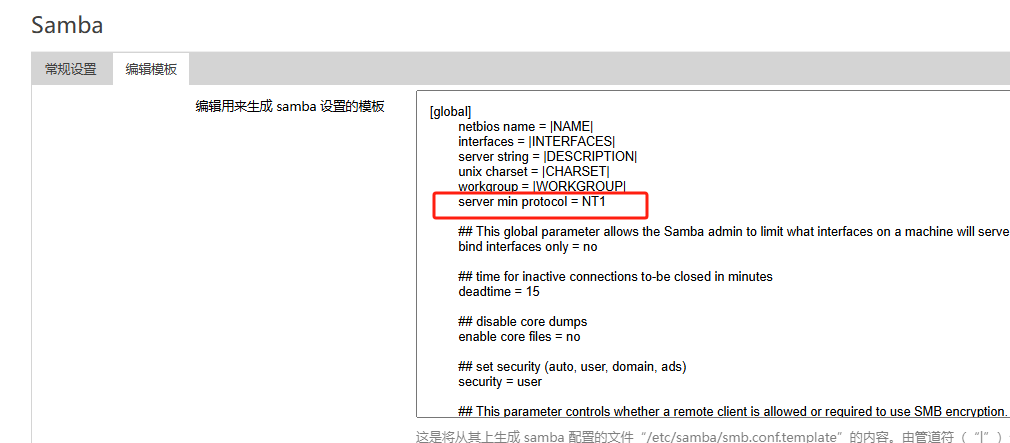
在其模板中添加server min protocol = NT1,确保最低访问协议是smb1,这是小米的必须条件。
7.测试服务。